In this digitalized era and with the excessive use of cloud services, there is a high chance that online hackers will attack your data and systems. One of the most prominent is the ransomware attacks. The hackers can get access to your sensitive information and files, and ask for a considerable amount of money to give back the access. The files are often removed and destroyed in other cases, but in the form of a Trojan or virus attack.
To get rid of ransomware, you must follow certain precautions and tools. We will be discussing this later in the article. Do you know? As per the Federal Bureau of Investigation (FBI), there are over 4000 ransomware attacks taking place every single day. Moreover, over $1 billion is the cost of ransom attacks and the amount paid to cybercriminals.
In this article, we will be learning in-depth about ransomware attacks, what are the types of ransomware and how to remove them.
What is a Ransomware Attack?
Ransomware is a type of malicious software that locks you out of your files and data or encrypts your files. Online hackers demand you pay a ransom to get a decryption key or access to the hacked file. The attack is so powerful that the hackers have the entire encryption key and information for that file or system taken over.
Understanding the Difference Between Ransomware & Malware?
Ransomware & Malware might seem the same, but they are different. Malware is an umbrella term for malicious software that hacks files and systems. Ransomware is a type of malware, but malware is not a type of ransomware.
Different types of malware attacks:
- Virus
- Ransomware
- Adware
- Trojan Horse
- Spambots
- Spyware
Talk to Our Cloud Security Experts to Know About Our Ransomware Protection
How Did Ransomware Start? Understanding It’s History
Ransomware attacks are not new. Businesses, governments, and even individuals have been victims of ransomware attacks for over three decades. The attacks became popular in the mid-2000s. However, the first recorded case of a ransomware attack occurred around 1989 when PC Cyborg was launched by an evolutionary biologist, Dr. Joseph Popp.
His method of infection was basic. He used to store the virus on disks said to contain sensitization programs on AIDS and sent the floppy disks to his victims. The Trojan-encrypted files activate on the victims’ computers when they try to play the disks. The system access gets locked.
So many things have changed since that first ransomware attack in 1989, especially in terms of sophistication and reach. The methods of dissemination, especially, have changed. The amount lost by organizations and individuals has also skyrocketed in the past few years. According to the National Security Institute (NSI), the average amount requested as a ransom fee rose to $200,000 in 2020 from $5,000 in 2018. This has brought to the question of how to remove ransom attacks across the globe.

Pop-up message for Ransomware Attack.
How Do Ransomware Attacks Take Place?
Ransomware attacks have been on the increase recently, mainly because cybercriminals consider them to be very lucrative. They can launch an attack easily, and compared to what they can make from it while expending minimal efforts, the margins look good, as many organizations would rather pay the ransom than halt their business processes.
A ransomware attack usually follows two steps, depending on the strain involved.
Data Encryption
Ransomware primarily uses data encryption software to encrypt the data in a system it infiltrates. The encrypted data becomes useless to the user without a specific decryption key, which can only be given by the attacker after a ransom is paid. The attack can cause huge losses to companies and business professionals.
Ransom Demand
Soon after the victim’s files get encrypted, a message on their screen demands that they pay a ransom to regain access to their files. The message would also contain instructions like how much ransom to pay, how to make the payment, and the deadline.

A glimpse of how hackers demand ransom. Source: Crowdstrike
How Does Ransomware Attack Your Systems?
There are many ransomware variants, but they are mainly delivered through:
1. Email phishing
Email phishing is the most common vector for propagating ransomware. These emails come with malicious links, attachments, or both.
It works in a way that any random user gets an email from someone they know that contains a malicious attachment, like a fake receipt or a fake order form. These attachments are executable files that look like Microsoft Office files or PDFs. If the user clicks on the attachment, the ransomware gets infected and is automatically downloaded into your system.
Similarly, the user can get an email with a link. You will be asked to fill in the credentials when clicking the link. If you do, the credentials get stolen and can be used to gain entrance and install the ransomware.
2. Remote Desktop Protocol (RDP)
In 2020 alone, enterprise networks experienced 3.3 billion RDP brute-force attacks. According to the Cyware report,1.4 million RDP brute force attacks were attempted daily by April 2020. An RDP is a Windows system protocol designed to give IT support access to control another system remotely to fix an issue. Unfortunately, this is the second most popular ransomware attack vector, as RDP ports are easily compromised.
RDP security is based on having a strong password protocol, and many users ignore this protocol. This makes it easy for hackers to penetrate vulnerable RDP ports and harvest their credentials. As soon as they succeed, they can then go past endpoint protection and begin to either wipe out data or encrypt it.
3. Malvertising
In this attack, malware is distributed by injecting malicious code into online advertisements and served to consumers through legitimate ad networks. If a user clicks on these ads, the corrupted code injected in the advert will install malware on your computer, or you may get redirected to a malicious website for an advanced attack. Unfortunately, malvertising attacks can happen even when the user clicks on the malicious links, making the attack more effective.

This is how a Malvertising attack looks.
What Happens When a User Mistakenly Clicks on the Link?
- The user is redirected to a malicious website that is different from the one in the ad.
- A JavaScript code to install malware on the user’s system is executed.
- Redirecting the user to a malicious website that looks like the real site but is operated by a hacker.
- Execution of an exploit kit - a malware designed to scan the system and exploit its weaknesses.
However, although less common, there are instances when the user doesn’t click on the malicious link, and may still get a malvertising attack. The most common occurrence is the drive-by download. In this case, the malware takes advantage of the vulnerabilities in your browser to secretly download and install the malware on your system even though you are viewing the ad without taking any action. This mostly occurs if your browsers and apps are outdated.
What are the Different Types of Ransomware?
Over the years, the meaning and attacking concept of ransomware has evolved. Here are the different types:
| 1. Crypto ransomware | |
|---|---|
This is the most common type of ransomware you will find globally. It uses complex algorithms to lock all or some of the data on the victim’s system, which cannot be unlocked without a decryption key. The key access is with the hacker, and can only be obtained after a ransom has been paid. |  |
| 2. Locker ransomware | |
This is one of the most common types of ransomware. The user gets blocked from logging in or accessing their files using non-encrypted malware. Payment is demanded from the user to regain access to their files. If you think about what ransomware does, remember that it blocks access to your files and data and demands a massive amount of money to give back your file access. |  |
| 3. Scareware | |
This type of ransomware uses scare tactics to compel the victim to pay the ransom. Like in the Locker ransomware attack, the victim’s files aren’t damaged. Instead, they get pop-ups with an official-looking seal like that of the FBI or the Department of Justice, telling them that they have broken a law and to avoid punishment, they should pay a fine. The amount asked is high and demanding. |  |
4. Leakware
This malware threatens to expose sensitive personal or company files to the public unless a ransom is paid. Leakware generally attacks public, private, and proprietary data and information. This usually leads to extortion because even if the victim pays the ransom, the attacker could demand more payment as they still have access to the files.
5. Ransomware as a Service (RaaS)
This type of malware is hosted by a professional hacker and offered on a pay-for-use basis. The hacker hosts and provides the ransom to criminals on the dark web as a subscription using the SaaS business model. After execution, a part of the loot is paid to the hacker based on their agreed-upon terms.
Want a Secure Cloud Now, With no Ransomware Fear
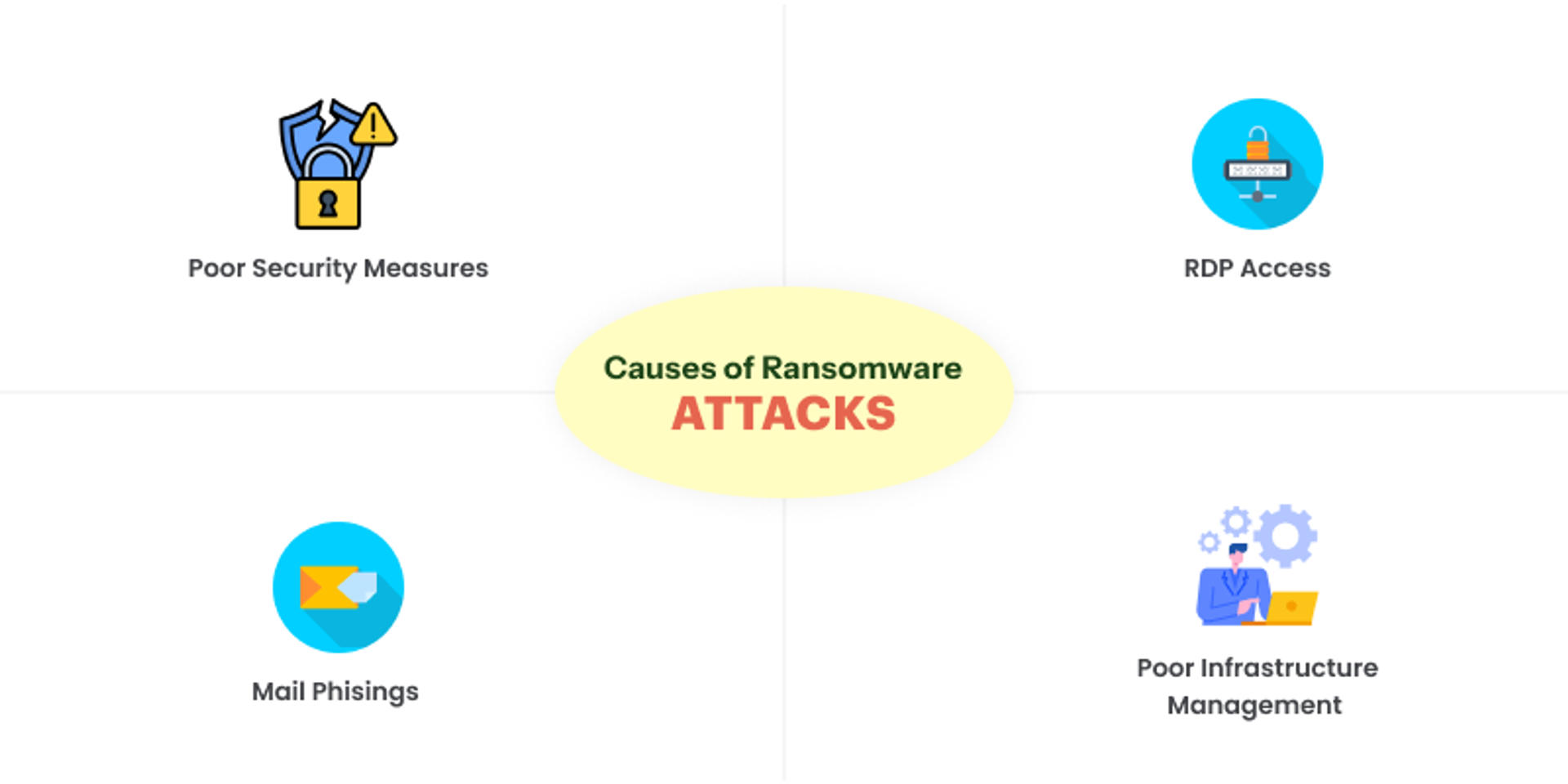
Causes of Ransomware Attacks
Most of the ransomware attacks are either targeted or randomly sent to individuals and companies through various mediums.
1. Poor Security Measures
If a user has little cybersecurity knowledge, they are prone to engage in poor security practices. For instance, if they have weak passwords, it becomes easy for any malicious actor to access their system and infiltrate the organization’s network.
To infiltrate and attack a system, a hacker needs only one staff member with little or no cybersecurity knowledge. When the staff in an organization doesn’t have the necessary cybersecurity training, the whole organization is vulnerable to ransomware attacks.
2. Mail Phisings
This is the most common cause of ransomware attacks. A survey by Fortinet reported that 1 in every 3,000 emails contains malware, including ransomware.
Hackers trick users into clicking a link or opening an attachment containing a malicious file. These files usually look like PDFs, Word documents, or ZIP files. Once the user clicks on it, it activates a script that downloads and executes the malware that either locks their systems or encrypts their files.
3. RDP Access
An RDP’s security depends on how strong the password protocol is, and often, users ignore these protocols. The easier the password, the easier it is to crack, which allows malicious actors to attempt to exploit it for their purposes.
Cybercriminals can use an open-source password-cracking tool to force the RDP password so they can log in as administrators. If they succeed, they gain full control of the system and activate the ransomware encryption program. This way, ransomware attackers will start demanding money to provide access.
4. Poor Infrastructure Management
Many ransomware attacks occur due to software infrastructure vulnerabilities. Every device has updates and patches regularly released to prevent exploits. If you have a poor habit of updating and patching your devices and apps regularly, they could easily be breached. You should have a robust security infrastructure and a maintenance technical team.
How Does Ransomware Affect Businesses?
Ransomware attacks can cause severe financial constraints and operational setbacks to businesses. Usually, the victim is asked to pay a huge ransom to regain access to their files or decrypt them. Furthermore, because of the attack, most business operations may have to be halted until the system is recovered and restored. One of the major setbacks of a ransomware attack is the loss of files and money.
List of Top Global Ransomware Attacks
1. JFS Foods Ltd
In May 2021, JBS Foods Ltd, one of the biggest meat processing companies in the world, got hit by a ransomware attack and had to stop operations at five of its largest plants in the USA. REvil, a popular and sophisticated Russia-based hacking group, executed the attack. On June 10th, it was confirmed that JBS paid the hackers a $11 million ransom in Bitcoin to stop the disruption and its impact on their supply chain constraints.
2. CNA Financial Services
On March 23rd, 2021, CNA Financial Services, one of the largest insurance firms in the US, fell victim to “a sophisticated cybersecurity attack.” The hacker group Evil Corp used the Phoenix Locker ransomware to encrypt 15,000 devices and more computers used by their remote workers. CNA Financial had to pay about $40 million as ransom to retrieve its data and restore its system. Ransomware attacks are not easy to handle for companies across the globe; they pay a lot, which degrades their status and trustworthiness.
3. Ascension Healthcare
Ascension is a healthcare company based in St. Louis. On May 8, 2024, Ascension was attacked by black Basta ransomware, targeting their digital health reports and communication systems. The attack leaked customers’ sensitive information, and Ascension had to pay a whopping $1.1 billion as ransom to stop the leakage.
4. CDK Global
The attack was made on 8th June 2024 at 15,000 US and Canadian auto dealerships. Their workflow was hampered by their inability to track inventory and process sales. The BlackSuit ransomware gang reportedly attacked it. The ransom given to the attackers was over $1 billion. This shows how grave and dark the ransomware attacks can be; they can destroy a company’s finances and reputation.
Ransomware Variants in 2024 - 2025
With the increase of remote work culture, it is unsurprising that the number of ransomware attacks has increased. We all rely on digital data transmission and cloud services, so various digital attacks in the form of ransomware, trojans, phishing, and virus attacks are common.
Here is the list of ransomware types in 2024.25.
| Ransomware Type | Market Share (%) |
|---|---|
| Lone Wolf | 9% |
| Akhira | 14% |
| Medusa | 5% |
| RansomHub | 14% |
| Qilin | 8% |
| Inc Ransom | 5% |

How to Avoid Ransomware Attacks?
The most effective way to prevent a ransomware attack is to combine technology and cybersecurity training. Here are some points to consider.

1. Engaging & Training End-Users
Since the targets are end-users, engaging with and training your employees on the threat ransomware poses and how it operates is crucial. Show them how to identify malicious emails. For instance, you can organize phishing simulations to teach them how to recognize and deal with phishing emails. Continually educating your employees will help them understand how to prevent and avoid potential ransomware attacks in the future.
2. Ensure to Scan & Verify Your Emails
You can never be too careful, and it is possible to slip up on a bad day and become a victim of one of the digital attacks. So, scan all incoming emails and authenticate them using the Domain Message Authentication Reporting (DMAR) and Conformance technology. Enable very strong spam filters to detect phishing emails. Filter all executable files and prevent them from reaching end-users.
3. Use a VPN for Public Wifi Use
Public Wi-Fi is usually not secure and is prone to interference. If you want to use public Wi-Fi, use a VPN. That way, your system will be protected even if an attacker performs a man-in-the-middle attack. Keep safe, keep vigilant on public connections and free wifi access.
4. Verify Links Before You Click on Them
Phishing emails are one of the most common ways ransomware attacks occur. You should never click on any link that looks suspicious, as a simple click can deploy ransomware into your system. This precaution also applies to email attachments. Verify email addresses and confirm the sender before opening any attachment. Double-check to ensure that the attachment you are about to click on is not a JavaScript or an executable (.exe) file. If you are unsure of a file or a link, forward it to IT support for sandbox tests.
5. Install Ad-blockers & Update Software Regularly
No matter how careful you are, ransomware can be deployed to your system through malvertising and drive-by downloads even when you don’t click any link. Installing ad blockers on your browser is the best way to prevent this from happening.
As simple as this sounds, it is the most basic preventive measure against ransomware attacks. No software or program is perfect. They always need to be updated and patched. Use a patch management tool to automatically deploy patches for your computers, networks, software, and operating systems whenever available. This will keep your files and systems safe from vulnerabilities.
6. Ensure Zero-Trust Principle
The principle of least privilege is a zero-trust principle. In other words, no user should have administrative access unless necessary. Instead, it grants users the minimum access to perform their tasks successfully. That way, nobody will mistakenly tamper with sensitive files. It is perfect for those companies that rely on cloud services and cloud hosting infrastructure.
7. Use Anti-Malware & Anti-Virus Programs
Use robust cybersecurity apps to block malware so it won’t even touch your system files. Some antivirus apps can block unsafe links, websites, and sketchy downloads. You can equally install whitelisting software to prevent the execution of unauthorized applications. Set these programs to conduct regular scans on your systems. This is one of the safest ways to get rid of ransomware.
8. Do Regular Data Backups
Many times, once a ransomware attack occurs, it is extremely hard, or in some cases, impossible, to successfully decrypt the encrypted files. Provide an offline backup to store your files and lock them. If possible, encrypt and isolate these backups to keep them safe from network breaches. Use a SAAE-18 compliant data center for backups and use a 256-bit encryption policy.
Want a Cloud With Enterprise Backup in Place
What Can the Possible Impact of a Ransomware Attack on Businesses be?
Here are the possible impacts of a ransomware attack on businesses and individuals. According to research, 64% of respondents felt their employer’s reputation suffered after the attack.

1. Workflow Disruptions
Ransomware attacks negatively affect a business’s productivity. Following an attack, all revenue-generating operations are usually put on hold until the system is secured and the company regains access to its files.
A good example is CDK Global. On June 8th, 2024, the company was hit by an organized cybersecurity attack. Due to the attack, CDK had to temporarily shut down its operations as it could not track inventory and process sales.
2.Massive Financial Loss
Although not reported, many organizations cave in and pay the ransom demanded. For big organizations, this usually runs hundreds of thousands to millions of dollars. For instance, when Colonial Pipeline was attacked in May 2021, the organization had to pay the hackers a whopping $4.4 million ransom.
3. Losing C-Level Employees
Many companies have been reported to lay off staff, especially C-level employees, after such attacks because of the losses they incurred. In some terrible cases, the organization had to shut down operations altogether. Layoffs are common during ransomware attacks as they weaken the company’s financial data.
4. Loss of Organizational Trust & Reputation
When organizations get hit by ransomware, it often affects their reputation and raises questions about their trustworthiness. Even though they are victims, most organizations keep ransomware attacks a secret and only tell their partners and sometimes customers because of the stigma attached to them.
Types of Ransomware Target Groups
There are two types of Ransomware target groups.
1. Spray and Pray Targets
This group represents the majority of ransomware attacks. Here, ransomware infections are spread through random vectors to unsuspecting victims. The actors often acquire a list of emails or compromised websites and attack them indiscriminately.
2. Big Time Player Targets
This second group, however, is specifically targeted, and a lot of research is done before they are targeted. They are usually big organizations with high-value assets, organizations that cannot afford downtime and can pay a high ransom. A typical example is the CDK case mentioned above.
Big time player targets organizations like:
- Any organization that can comfortably pay the ransom.
- Organizations that have loopholes in their cybersecurity infrastructure.
- Have a pain point that the hackers can squeeze to make them pay the ransom.
Prime Targets for Ransomware Attackers:

1. Healthcare Infrastructure
It is estimated that 45 percent of ransomware attacks target healthcare organizations. According to a report by Emisoft, about 560 healthcare facilities were affected by ransomware attacks. Hospitals, medical clinics, testing centers, and other healthcare organizations can’t afford downtime or locked systems. They always need access to electronic medical records to administer and monitor patients. This makes them more likely to pay a ransom, so they are top ransomware targets.
2. BFSI sectors (Banking, Financial Services & Insurance)
The BFSI sector is also a prime target because it is where the money is. Banks have been experiencing an increase in ransomware attempts and phishing emails due to the deep penetration of digital banking features and options. Often, ransomware attacks in the financial sector do not result in encrypted data but the theft of sensitive data. The victims are then threatened to pay the ransom or risk having their data published online.
3. Education Sector
A report by BlueVoyant revealed that universities experienced a 100 percent increase in ransomware attacks between 2019 and 2020, and the number of attacks is expected to grow in the coming years. Universities, colleges, public district schools, and trade schools are all targets of ransomware, as they store sensitive student data and do not want their classes disrupted.
4. IT sector
Reports have revealed that the IT sector experienced a significant increase in ransomware attempts in recent years. Because of digitalization and remote work culture, many organizations have implemented remote work models, making it easier for attackers to explore gaps in their cybersecurity and locate vulnerabilities. Hackers usually deploy malicious emails to disarm victims in the IT sector, infiltrate their systems, and encrypt their data.
5. Manufacturing Industries
Attackers usually target manufacturers because most run factory operations around the clock and can’t afford to have them disrupted. They would rather pay the ransom than allow disruptions affecting the supply chain. Industrial organizations with industrial control systems (ICS) that control physical equipment in their operations are also prime targets. Hackers can easily hold their critical infrastructure hostage and pressure them into paying hefty ransoms.
Build Your Ransomware Shield: Start Protecting Your Assets!
How to Remove Ransomware Attacks: A List of Measures to Take

In case of any ransomware attack, you can take these steps:
1. Isolate the Infected Device or PC
You must identify the affected system and quarantine it immediately. Turn off all the machines that could have been potentially affected by the ransomware, isolate them, and disconnect them from your network. This will prevent the ransomware from spreading and infecting the network or shared drives. It will also give you ample time to recover data, contain the damage, and prevent the condition from worsening.
2.Keep Backup Secure
Make sure you have a secure backup centre. If infected, at this point, secure your backup systems and take them offline. Before you do so, make sure they are free of malware. Always have SAAE-18 compliant data centers, which are secure & safe.
3. Contact Govt. Law Enforcement Agencies
As soon as you discover that you are a victim of a ransomware attack, notify the local law enforcement and any of the field offices of the U.S Secret Service or the Federal Bureau of Investigation (FBI) immediately, and ask them to assist you. They will help you get out of the digital blunder with their exercise.
4. Identify Ransomware Attack & Try to Remove with Antivirus Tools
Your response to crypto-ransomware will differ from that to locker ransomware, so identify what you are dealing with. Knowing what kind of cyber attack you are a victim will help you get out of it. If the ransomware you are dealing with is the locker ransomware and not the crypto-ransomware, you can get rid of it and regain access to your system. Moreover, you can use antivirus tools and programs to remove malware and trojans.
5. Identify the Source of Attack & Safeguard
Even if you decide to abandon the encrypted data, you will still have to deal with the infection and prevent it from spreading further. First, you must identify how it happened and tighten that loose end to prevent a second occurrence. This could mean changing all your online account passwords and all system passwords as soon as the malware is removed.
Should You Pay Ransom to Digital Attackers?
If your system has been compromised, you’d be willing to pay the ransom, especially if it is a little compared to the potential losses you could incur. However, you must understand that the people you are dealing with are criminals and may just take your money and run. It is not advisable to pay the ransom because there is no guarantee that the encrypted files will be decrypted. The criminals could even decide to keep extorting you. A report stated that 80% of victims who paid ransom demands were exposed to a second attack.
Some sources say that the FBI does not support paying a ransom in response to a ransomware attack. Paying a ransom doesn’t guarantee you or your organization will get any data back. It also encourages perpetrators to target more victims and incentivizes others to get involved in this illegal activity.
Concludingly: What is the Future of Ransomware Fixes?
There is no permanent solution for ransomware attacks. The best you can do now is protect your networks and ensure you don’t become a victim. You must continuously educate your employees, for instance, to help them understand how ransomware works and how they can prevent an attack from succeeding. New ransomware attacks are already on the rise due to the massive digitalized web space. We have to learn about what ransomware does and how we can tackle its threat. There are many types of ransomware, and we must keep an eye on each of them and their evolution.
In conclusion, you can no longer choose to be on the sidelines if you wish to be safe. You must take cybersecurity more seriously and invest in it as a matter of course. You must always be vigilant and never take software updates for granted. If every organization takes cybersecurity more seriously, these attacks will rapidly decline.
Frequently Asked Questions
What do you mean by ransomware?
A ransomware attack is malicious software designed to infect systems and devices that restrict your access to files, networks, or computers.
How do I know if I have ransomware?
If your systems and devices behave abnormally, they are infected with ransomware. Your computer will slow down, network errors will start, and you will not be able to access your files and data. Random pop-up messages may also appear demanding actions. This is a typical symptom of a ransomware attack.
Can ransomware be deleted?
Yes, ransomware can be deleted, but it depends on how quickly you respond and what measures you take to remove the ransomware stain. You can disconnect your systems and use anti-malware and virus tools.
What happens if you don’t pay the ransomware?
If you don’t pay the ransomware attackers, your data and files will most likely remain encrypted. And you will not be able to access your files until you get the decryption key.
What happens if you are attacked by ransomware?
If you are attacked by ransomware, your files, system, and data will not be accessible. All your data information files will be encrypted, and ransomware attackers will start demanding money to decrypt the files and allow access.
Can you fix a ransomware attack?
You cannot guarantee a fix for a ransomware attack. However, you may have a chance if the attacker gives you the key to access after a monetary payment.
What is a ransomware cyber attack?
A ransomware attack is a cyberattack in which malicious ransomware software infects the user’s system and files, denying the user access to files and systems.
Is it possible to prevent a ransomware attack?
You cannot fully prevent a ransomware attack, but you can take measures to prevent it from infecting your systems.


